Stefano Zanero received a Ph.D. degree in Computer Engineering from the Politecnico of Milano university, where he is currently an associate professor. His research interests focus on systems security: web application security, computer virology, malware analysis, underground economy, and in general data analysis applied to security. He has been a speaker at international scientific and technical IT conferences such as Black Hat, Hack in the Box, and CanSecWest. Besides co-authoring books and scientific articles on information security, he is on the editorial board of the “Journal in Computer Virology” and has also been the author of the “Security Manager’s Journal” column on Computer World Italy, for which he has won a journalism award.
Since 2004 he has been partner of Secure Network, a market leader in Italy for penetration testing and boutique security consulting, based in Milan. In 2011 he co-founded a firm specializing in cloud-based applications for mobile ticketing.
Stefano what are the key political, ethical challenges we face in cyber world in these days, when information is widely available and privacy is
intruded upon?
This is such a huge and important question. The challenges are multi-faceted, I’ll try to focus on a few key points. As a society, we are increasingly relying on digital systems for our lives. Critical infrastructures are supported by digital technologies, our social interactions flow through the Internet, and our businesses are supported by and in an increasing number of cases constituted by a flow of digital information. This creates an unprecedented level of exposure to different types of threats: criminal activities targeting money and businesses; large-scale espionage and profiling, conducted by both companies and governments; finally, the looming issue of cyberwarfare and cyberterrorism. Criminal activities do not raise much of an ethical challenge (except in some gray areas such as misguided proposals to “hack back” responding to intrusions). But large-scale privacy invasion and cyberwarfare both raise significant questions. What is the role of engineers? For IEEE members, for instance, the Code of Ethics clearly states that beingimplicated in invasive surveillance (for commercial or governmental organizations alike) is unacceptable.

Ethically, we should as engineers always strive to design system with privacy safeguards built in. We should minimize the possibility that our work exposes citizens to danger. Cyberwarfare is an even more difficult area. Is conducting intelligence or military operations through the means of cyberattacks an ethically acceptable proposition? This is very different from the traditional – and socially accepted – role of engineering in developing weapon systems: this is an active, operational role, with its very own challenges. Politically, the current high-profile challenge is the development of legislation (such as, for instance, the Wassenaar Arrangement) to curtail development and export of intrusion software as a dual-use, military implement. While on surface a reasonable idea, this raises many challenges and dangers for the research and engineering community. My co-chair in the STC for Cybersecurity and I, along with other valiant colleagues, have authored several position papers on the subject that you can find here: http://www.cs.dartmouth.edu/%7Esergey/wassenaar/
Could you elaborate more on your current research areas?
I work in the area broadly known as systems security (and nowadays often called “cybersecurity”), which means applied computer security. My specific key areas of work are automated, large scale malware analysis and threat intelligence. In brief, I try to use machine learning and data analysis techniques to make sense of large datasets of attack and threat data (which often entails building the sensors and the observation networks to gather the data in the first place!).
As founding member of ISSA Chapter in Italy in 2005, how do you evaluate the growth and progress of the organization? How much of an impact has it being able to achieve?
ISSA has been growing throughout Europe, not just in Italy, in the past 10 years. But I would honestly say that entering ISSA and taking on volunteer roles (besides the chapter, I have been elected and still sit in the International board of the organization) had a big impact on my own career as well! The organization basically reinvented itself in the past 8-10 years, and I feel privileged to have been part of its leadership team along with well-known luminaries of the field.
What is your inspiration behind taking up Cyber Security as your area of study?
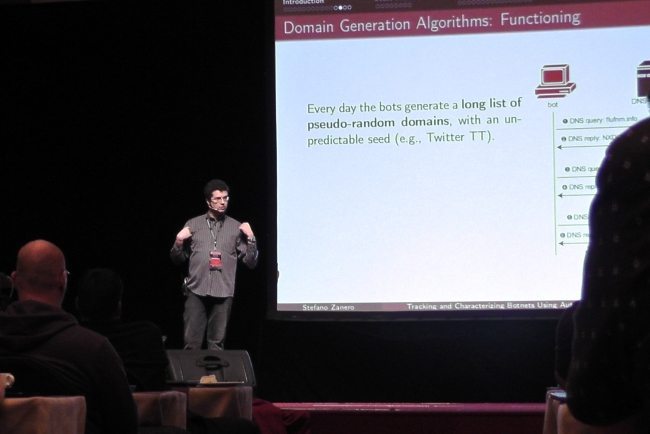
That’s a very good question. I got hooked with security issues (on the small, obviously) in 1997, and have been playing with it ever since. I was just starting university at that time, and security was really not that much developed academically in Italy. I learned on my own, and pursued artificial intelligence and machine learning as my main academic area. Then, selecting my thesis topic, I proposed to my advisor to apply machine learning techniques to intrusions. He was happy to test algorithms on a problem that was novel for him, and I was glad to join my academic courses to my interest. Then, over the years, the “security” part took by far precedence over the “AI” part of my training, and… here we are. Taking part in hacking conferences all around the world helped shape my hands-on, applied approach to the problem. And it also helped build me an exciting network of friends and peers, before I was able to build my own research group at Politecnico.
Among the many conferences you’ve been a part of, which one would you rate as the best and why?
Academically, surely the best conference in the area is our own IEEE Security and Privacy Symposium, also known as “Oakland” among our constituency. That’s were the top research is presented and the top researchers network and mingle. It’s an experience that any student or researcher in the area should try to make at least once. Our field is peculiar in having a lot of non-academic, hacking-based conferences. Of these, the flagship event is surely the Black Hat conference in Vegas every year, side-by-side with Defcon, with more than 13.000 and 18.000 people respectively. It is a whirlwind of connections, partying and in-depth information talks and labs. A yearly pilgrimage to see what’s new, to reconnect with the community and to meet lifelong friends from all over the world.
Interview conducted by Alina Benny and Aparna Sekhar